Anita lost ₹47,000 on a Tuesday afternoon in March.
Someone called claiming to be from the electricity board. Her bill was overdue, they said. If she didn’t pay immediately, they’d cut the connection. She panicked — she works from home, she needs the WiFi — and followed instructions to “verify” her account through a UPI collect request.
By the time she realized what had happened, the money was gone. She stared at her phone for a few minutes, then did what most people do: she called her bank.
The bank’s customer care line put her on hold for eleven minutes. When someone picked up, they told her to raise a complaint through the app. She asked them to reverse the transaction. They said they couldn’t. She asked who could. They told her to file an FIR, call 1930, and also register a complaint on the cybercrime portal. Three different places. Three different processes. Nobody told her what would happen next or how long any of it would take.
Here’s the thing that tripped Anita up, and trips up almost everyone in her situation: she assumed her bank could just pull the money back. That’s how credit cards work, right? You dispute a charge, the bank reverses it. She thought UPI would work the same way.
It doesn’t. And the reason it doesn’t is the thing most people never learn until they’re already 45 days deep into a process that was never built for their problem.
Last week we talked about fraud detection — the system that tries to stop bad transactions before they happen. This week is about what happens when that system fails. The transaction went through. The money left your account. Now what?
It depends on what kind of “wrong” happened. And most people find out too late that there are two answers, not one.
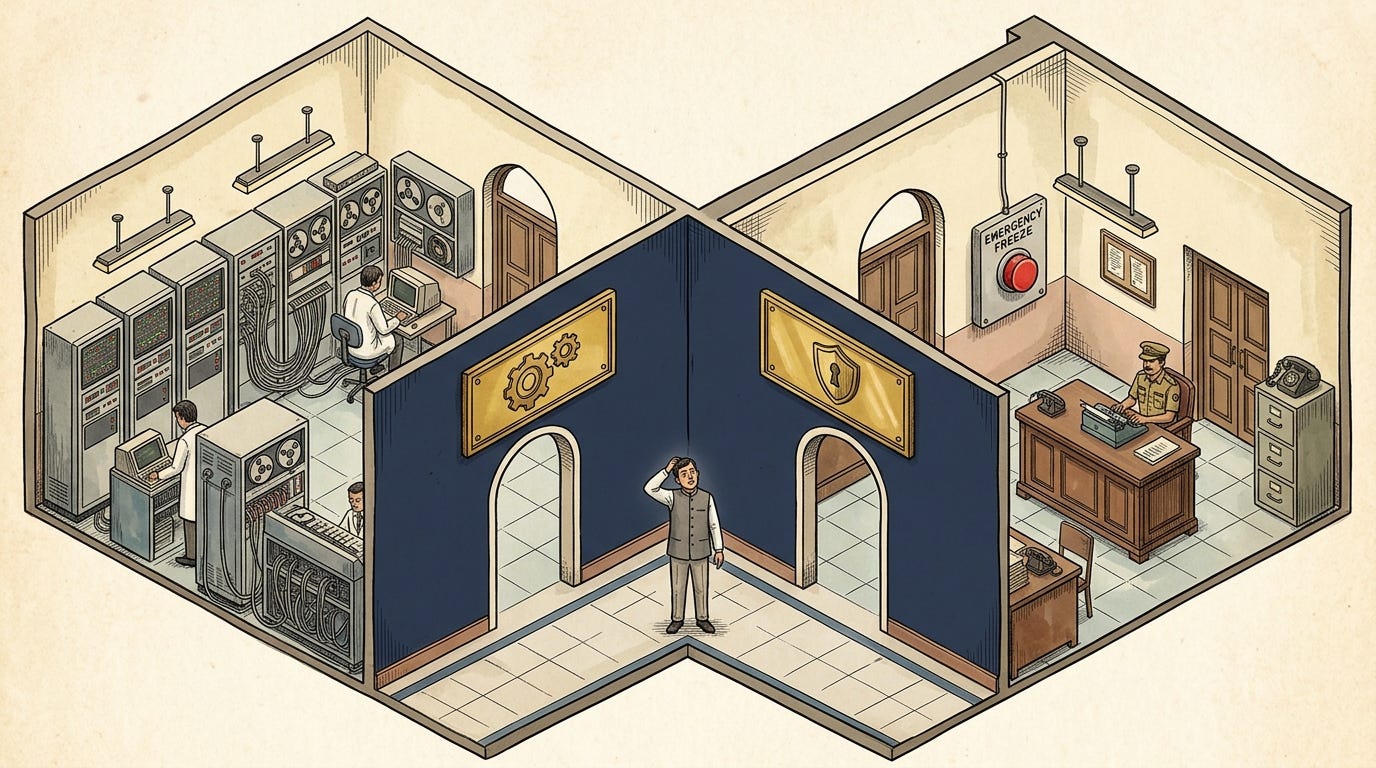
Two machines, two problems
There are two recovery paths in India’s digital payment system, and they have almost nothing to do with each other. Banks rarely explain this. Most people figure it out only after they’ve spent weeks going down the wrong one.
Machine 1: the chargeback (UDIR)
This is NPCI’s Unified Dispute and Issue Resolution system, launched in 2020. It handles technical problems. Your payment was debited but didn’t reach the merchant. You got charged twice for the same transaction. A payment timed out but the money left your account. In these cases, your bank can initiate a chargeback — a formal reversal request routed through NPCI to the recipient’s bank.
For these technical failures, the system has gotten quite good. Before UDIR, banks communicated through manual, file-based processes. A stuck payment could take days just to begin investigating. Now, many of these cases auto-resolve within hours. NPCI reports resolution times have improved by roughly 50% since UDIR was introduced.
The chargeback path also covers merchant disputes — you paid for something and it never arrived, or the merchant charged the wrong amount. These take longer (turnaround times run up to 30 days for small and offline merchants) but the process exists and broadly works.
Machine 2: the police freeze (CFCFRMS/1930)
This is what you actually need when you’ve been scammed. And it works completely differently.
When Anita sent money to a scammer, she authorized the transaction. She entered her PIN. From the bank’s perspective, this wasn’t a technical failure or a merchant dispute. She voluntarily transferred money to another person’s account. A chargeback can’t help her — her bank legally cannot reach into the scammer’s account and pull the money back from an authorized P2P transfer.
What can help is the 1930 helpline and the CFCFRMS (Citizen Financial Cyber Fraud Reporting and Management System). When you call 1930, the operator sends an emergency freeze request — a lien — to the beneficiary’s bank. Under police authority, that bank freezes whatever funds are still sitting in the account. The goal is to stop the money before it moves further.
But here’s the catch: even if 1930 successfully freezes the funds, getting that money back into your account usually requires a court order. Some states — Gujarat, UP — have set up faster processes through Lok Adalats or nodal police orders. Others haven’t. So “frozen” doesn’t mean “returned.” It means “stuck in a legal process that could take months.”
Anita didn’t know any of this. She walked into her bank expecting Machine 1 (chargeback — reverse the payment) when she actually needed Machine 2 (police freeze — stop the money, then get a court order). Her bank’s customer care agent didn’t explain the difference. Most don’t.
The golden hour
There’s a term that keeps coming up in cybercrime circles now: the golden hour. The I4C (Indian Cyber Crime Coordination Centre) borrowed it from emergency medicine, where treatment within the first 60 minutes after trauma dramatically improves survival. In fraud recovery, the math works the same way.
If you call 1930 within the first hour of losing money, the chances of freezing the funds before they move are reasonably good. After that first hour, they drop off sharply.
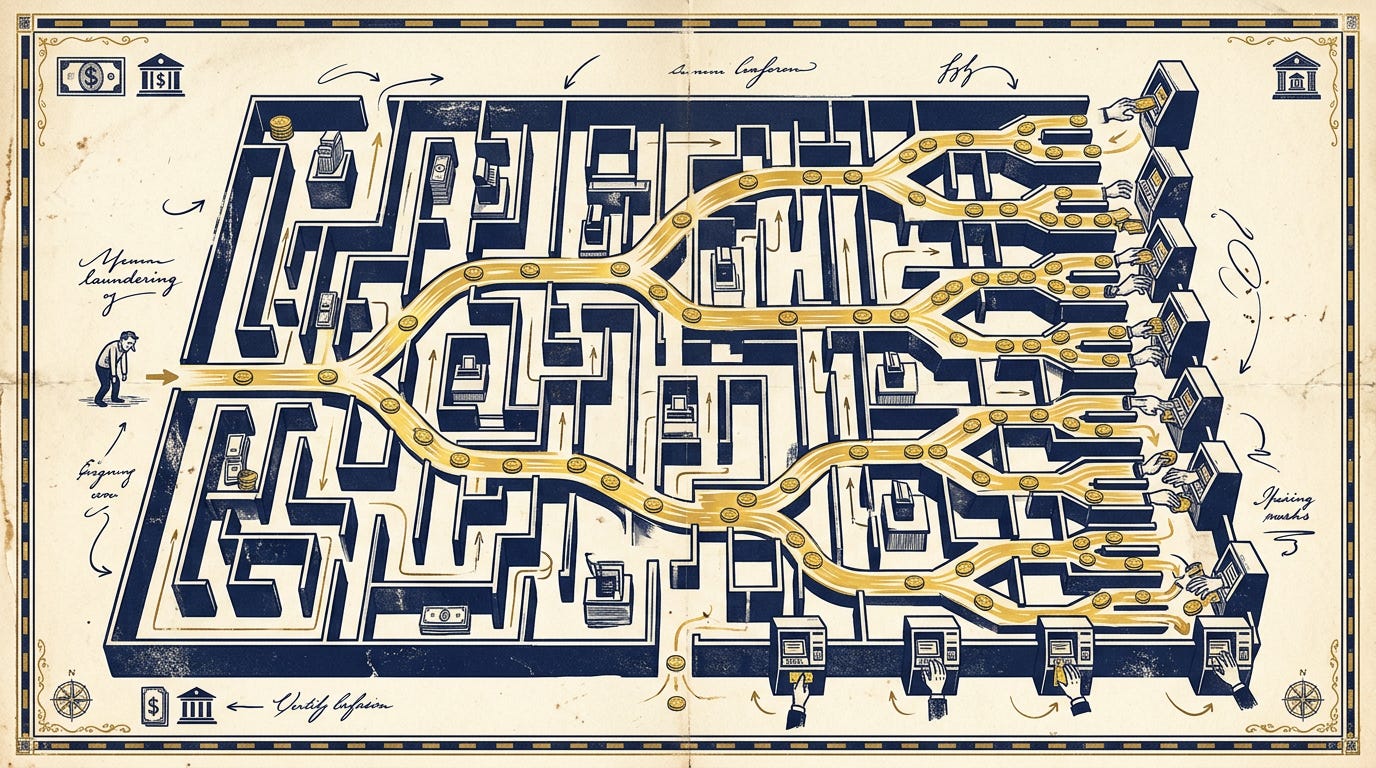
Why? Because fraudsters don’t leave money sitting in the account you sent it to. Within minutes, they split the amount across multiple accounts — mule accounts, often opened using rented bank credentials or forged KYC documents. The money gets layered through three, four, five hops and withdrawn as cash from ATMs in a different city. By the time your complaint reaches someone who can act on it the next morning, the account is empty and the trail is cold.
In 2025, the 1930 helpline received 3.24 crore calls. Mumbai’s helpline alone saved roughly ₹202 crore through rapid intervention. Nationally, the CFCFRMS system has saved over ₹7,100 crore across more than 23 lakh complaints since it launched.
Those numbers sound large until you set them against the ₹28,683 crore lost to digital fraud that same year. The system saved roughly a quarter of what was stolen. For every rupee recovered, three disappeared.
And that’s assuming you called at all.
Why half the victims stay quiet
Roughly half of UPI fraud victims never report the fraud. When you first hear that number, the instinct is to wonder what’s wrong with them. Why wouldn’t you report it?
Spend five minutes trying to navigate the reporting process and the number starts making sense.
There’s the shame. Most UPI fraud is social engineering — someone talked you into sending money. You weren’t hacked. Nobody broke into anything. You were convinced. Telling a stranger on a helpline that you fell for a fake electricity board call feels embarrassing, especially when you can hear them thinking “how did you fall for that?”
Then there’s the fragmentation. You’re told to call 1930, file a complaint on cybercrime.gov.in, raise a dispute in your UPI app, and file an FIR at your local police station. Four separate systems. The cybercrime portal asks for your transaction ID, the UTR number, the beneficiary’s VPA — details most people don’t know how to find on a good day, let alone while panicking.
Dvara Research studied the in-app complaint experience across six major UPI apps. Only four of the six even let you raise complaints inside the app. The other two sent you to external helplines. In the apps that did have complaint filing, the option was “placed obscurely in a corner at the top or bottom of the screen,” sometimes hiding behind other options, three taps deep from anywhere you’d naturally look.
And then there’s the math. If you lost ₹2,000 to a fake collect request, you do the calculation: is it worth three hours of my evening navigating a system that probably won’t return the money? For a lot of people, the answer is no. They absorb the loss and move on.
The reporting system was designed by people who understand how it works. It wasn’t designed for the person using it at 11 PM while their hands are shaking.
Anita’s 45 days
Let me walk through what actually happened to Anita after she lost that ₹47,000.
On day one, she called her bank, got told to use the app. She raised a dispute in the app. She also called 1930 and filed a complaint on cybercrime.gov.in. Three complaints, three systems, none of them talking to each other. She went to her local police station to file an FIR. The officer asked if she could come back tomorrow because the person who handles cyber complaints wasn’t in.
By day three she’d filed the FIR and gotten a complaint reference number from 1930. No update from her bank.
Day seven, her bank acknowledged the complaint. “Investigating.” No details on what that meant or what they were investigating.
Two weeks in, she called again. They said a chargeback had been raised with the beneficiary bank. (This was already the wrong tool — chargebacks don’t apply to authorized P2P transfers. But nobody told her that.)
Day thirty: the beneficiary bank responded. The funds had already been withdrawn. The account had been closed. Chargeback declined.
Day forty-five: her bank told her that since the transaction was “authorized” — she had entered her own PIN — they couldn’t process a reversal. They suggested she continue pursuing the case through the cybercrime portal and the courts.
Anita never got her money back.
Meanwhile, the 1930 freeze she’d triggered on Day 1 had actually worked — partially. The system froze about ₹11,000 in the scammer’s account before the rest was moved. But releasing even that ₹11,000 back to Anita required a magistrate’s order, which, three months later, she was still waiting for.
She spent 45 days going through a chargeback process that was never designed for her situation, while the process that could actually help — the police freeze and court recovery — moved on its own, slower timeline with no connection to anything her bank was doing.
This is the standard experience for social engineering fraud on UPI. Not an edge case.
Why chargebacks can’t fix social engineering
The chargeback system was built for a specific world: one where the main dispute is “I didn’t make this transaction” or “I paid a merchant and didn’t get what I ordered.”
In that world, the logic is clean. Either the transaction was authorized or it wasn’t. If it wasn’t, the bank bears liability — RBI’s July 2017 circular on customer protection says that for unauthorized transactions reported within three working days, the customer’s liability is zero. The bank has to credit the amount back within ten working days.
If someone hacks your account, clones your SIM, compromises your device — that’s an unauthorized transaction. The bank pays. And banks invest heavily in preventing this, because it costs them money.
But most UPI fraud doesn’t look like that. Most UPI fraud is social engineering. The caller claiming to be from your bank. The fake KYC update. The “digital arrest” scam where someone impersonates a police officer on video call. The investment group on WhatsApp promising 3x returns.
In every one of these cases, the victim enters their own PIN. The transaction is, technically, authorized. If a hacker breaks into a vault and takes your money, the bank pays. If a scammer politely convinces you to open the vault and hand them the money, you pay. The system only cares that you turned the key. It doesn’t ask whether you were lied to about what was on the other side.
India hasn’t created a mandatory reimbursement framework for this kind of fraud. The UK has — their Payment Systems Regulator made APP (Authorized Push Payment) fraud reimbursement mandatory in October 2024, with the cost split between the sending and receiving banks. Indian consumer advocates have been pushing for something similar. So far, it hasn’t happened.
Until it does, the gap between “unauthorized fraud” (system works) and “authorized fraud under manipulation” (system doesn’t work) is where most of the damage sits.
What’s actually getting better
Some of this is getting better, though.
UDIR has made technical dispute resolution dramatically faster. Double debits, stuck payments, timeout errors — these used to require manual coordination between banks that could drag on for days. Now many resolve automatically within hours. If your payment went out but the merchant says they never received it, the system handles that reasonably well.
The 1930/CFCFRMS layer has created a real-time fraud response that didn’t exist five years ago. The golden hour framework has saved thousands of crores. UP’s Cyber Fraud Mitigation Centre — where police and bank nodal officers sit in the same room — pushed recovery rates from around 25% to nearly 89% between September 2025 and March 2026. The difference wasn’t better technology. It was putting the people who could act in the same physical space and cutting the communication lag from days to seconds.
Mumbai’s 1930 centre saved ₹202 crore in 2025 alone, largely through immediate account freezes coordinated from a 50-person call centre in Bandra that operates 24/7.
The RBI’s proposed Kill Switch from the April 2026 discussion paper could give users a way to freeze their own outgoing payments instantly — a panic button you can hit before you even need to call anyone.
And NPCI’s July 2025 chargeback reform (RGNB — allowing banks to re-raise genuine chargebacks that were declined due to caps) acknowledged that the earlier cap system had swung too far toward preventing abuse and was blocking real complaints.
But the structural hole remains. For social engineering fraud — the kind that causes the most damage — there’s no clear liability framework saying the bank has to make you whole. Recovery depends on whether you called 1930 fast enough, whether the freeze caught any money, whether the courts in your state have a quick process for releasing frozen funds, and whether you have the persistence to follow through for months.
That’s a lot of things that have to go right, and very few of them are in your control.
What this tells you about where we are
The dispute resolution infrastructure for digital payments in India was built for an earlier version of the problem. An era where the main thing that could go wrong was a technical glitch — money stuck in transit, a double debit, a server timeout. For those problems, the system works well and is getting better.
The problem moved. The majority of losses now come from social engineering, and the recovery infrastructure hasn’t caught up. There are two separate machines — chargebacks for technical failures, police freezes for fraud — and most victims don’t know which one to use. The machines don’t talk to each other. And the one that matters most for fraud (the police freeze) ends in a court process that most people can’t navigate alone.
A 72-year-old in Lucknow who sends ₹1.8 lakh to a scammer under duress isn’t “authorizing” anything in the way that word should mean. But the system treats the transaction as if he walked into the bank, filled out a withdrawal slip, and handed someone the cash. The legal framework hasn’t caught up to the reality that consent under manipulation isn’t really consent.
That gap — between what the system was built for and what it’s being asked to handle — is where the next round of reform will have to focus. Whether it comes from RBI mandate, NPCI policy, or the courts, someone is going to have to decide who pays when a person gets tricked.
Next week
So far we’ve covered money moving fast, how it gets authenticated, how fraud is caught or missed, and what happens when you try to get your money back.
Next week, we step back from the crisis and look at something less dramatic but just as load-bearing: KYC and compliance. The paperwork underneath all of this. Why you had to submit your Aadhaar and PAN to open a bank account, what your bank actually does with that information, and why the “Know Your Customer” process is both the foundation and the bottleneck of India’s financial system.
There’s also a direct connection to what we just covered: the reason scammers have so many mule accounts to launder money through is, in part, a KYC problem. Forged documents, rented accounts, incomplete verification. The leaks in the identity layer feed directly into the fraud we spent two weeks discussing.
How Money Moves · Week 11 of 52